Last but not least: in order to get change to happen in the government, assuming you don’t have enough money to buy whatever change you want, you need to get society riled up. Snowden did a great job at this, because he illustrated for the country what was being done, and had the credibility to do so, rather than just saying, “yeah, the government is doing all this bad stuff” like many of us have assumed for years.
But, the spread of an idea happens not because the media talks about it, but because families talk about it at the dinner table, co-workers at the water cooler, Redditors bitch and moan on the Internet, etc. No matter how big your “megaphone” is, it is not bigger than the millions of small voices working together. Discussing your concerns and sharing with those who, perhaps, don’t understand why this is a problem, why this is a problem, is so important.
If you’d like to share things they can do to protect their privacy, here’s an index of this series (share this post to share the index, or pick a post and share the direct link):
- No Surveillance State Month, Part 1: Turn Off Your Cell Phone
- No Surveillance State Month, Part 2: VPN for Privacy
- No Surveillance State Month, Part 3: Online Database Opt-Out
- No Surveillance State Month, Part 4: Ditch the Plastic
- No Surveillance State Month, Part 5: Anonymous Electronic Payments
- No Surveillance State Month, Part 6: TrueCrypt & Full Disk Encryption
- No Surveillance State Month, Part 7: Encrypted Phone Calls
- No Surveillance State Month, Part 8: Encrypted Text Messages
- No Surveillance State Month, Part 9: Don’t Trust Bad Certificates
- No Surveillance State Month, Part 10: Low Tech Password Security
- No Surveillance State Month, Part 11: Tor — Peer-to-Peer Encrypted Traffic
- No Surveillance State Month, Part 12: Try for SSL
- No Surveillance State Month, Part 13: Update Your Software
- No Surveillance State Month, Part 14: App Awareness
- No Surveillance State Month, Part 15: Encrypt Your E-mails
- No Surveillance State Month, Part 16: Encrypt Your Phone
- No Surveillance State Month, Part 17: Give Facebook Less Info
- No Surveillance State Month, Part 18: Avoid Social Engineering Attacks
- No Surveillance State Month, Part 19: Use Friendly Web Services
- No Surveillance State Month, Part 20: Snail Mail Services
- No Surveillance State Month, Part 21: Password Questions Are the Devil
- No Surveillance State Month, Part 22: Archive Your E-mail
- No Surveillance State Month, Part 23: Hunting Malware
- No Surveillance State Month, Part 24: The Smell of Packets
- No Surveillance State Month, Part 25: Local Big Brother
- No Surveillance State Month, Part 26: Big Brother on the Road
- No Surveillance State Month, Part 27: Third Party (“Tracking”) Cookies
- No Surveillance State Month, Part 28: Tweet Companies Who Abuse Your Privacy
- No Surveillance State Month, Part 29: Contact Congress
- No Surveillance State Month, Part 30: Start a Conversation
It’s been an exciting month. I started this series before the Snowden leak, and it just so happened to have perfect timing. I hope it’s raised a little bit of awareness of how we’re all tracked and what we can do to stop it.
This is one of a 30-part series, “No Surveillance State Month,” where daily for the month of June I’ll be posting ways to avoid invasion of your privacy in the digital age. The intent of these posts is not to enable one to escape detection while engaging in criminal activity — there’s still the old-fashioned “send a detective to watch you” for which these posts will not help. Rather, this series will help you to opt-out of the en masse collection of data by the government and large corporations that places Americans in databases without their knowing and freely-given consent for indefinite time periods. We all have the right to privacy, and I hope you demand it.
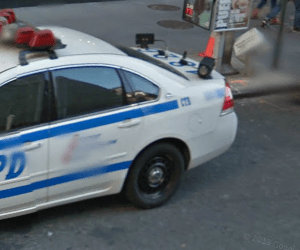 Our last post covered how local governments can track you walking on the streets. It doesn’t get much better for other modes of transportation. Consider:
Our last post covered how local governments can track you walking on the streets. It doesn’t get much better for other modes of transportation. Consider: