 Our last post covered how local governments can track you walking on the streets. It doesn’t get much better for other modes of transportation. Consider:
Our last post covered how local governments can track you walking on the streets. It doesn’t get much better for other modes of transportation. Consider:
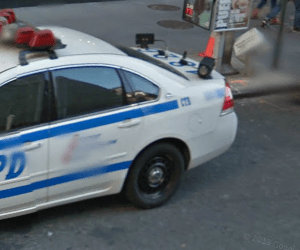
- Do you drive? Mind the license plate readers (pictured) tracking you and putting you in a database every time you pass by. This man submitted a FOIA request for the records collected on his car and found that his location had been logged (and photographed!) 112 times.
- On the highway? If you use E-ZPass, SunPass, or any other prepaid toll system, each trip you make is logged. They can potentially even use this data to show how fast you were going by timing your passage between two points.
- Taking a train? Bought your ticket on your credit card? Or worse, bought a fare card (Metrocard, etc.), which records every swipe?
- Taking an airplane? lol 🙂 You know the deal already.
All of these pieces of what the NSA would call “metadata” can be pieced together. You buy a fare card on your credit card, and they know who you are. You swipe it at a turnstyle, and there’s a camera there being recorded and retained. Your entire journey can be watched, and as facial recognition increases, their ability to have a computer follow you from camera to camera increases.
Scary, isn’t it?
What can you do? The #1 lesson here seems to be pay in cash. It’s much harder to track your every step if you don’t broadcast your entry into the dragnet with a credit card swipe. On the road there are nifty little license plate covers designed to make your plates harder to photograph (an example I found on Google). But remember, we should be fighting against these systems before they’re implemented. 🙂
This is one of a 30-part series, “No Surveillance State Month,” where daily for the month of June I’ll be posting ways to avoid invasion of your privacy in the digital age. The intent of these posts is not to enable one to escape detection while engaging in criminal activity — there’s still the old-fashioned “send a detective to watch you” for which these posts will not help. Rather, this series will help you to opt-out of the en masse collection of data by the government and large corporations that places Americans in databases without their knowing and freely-given consent for indefinite time periods. We all have the right to privacy, and I hope you demand it.
 The New York Post has persisted in running covers condemning whistleblower Edward Snowden as a man who has betrayed America. If by “America” they mean “the government of the United States while engaged in a a sneaky, immoral, and illegal program designed to spy on its citizens,” then perhaps they are right. But if they mean “America” as in “the people of the United States,” they are dead wrong.
The New York Post has persisted in running covers condemning whistleblower Edward Snowden as a man who has betrayed America. If by “America” they mean “the government of the United States while engaged in a a sneaky, immoral, and illegal program designed to spy on its citizens,” then perhaps they are right. But if they mean “America” as in “the people of the United States,” they are dead wrong. There are better ways he could have blown the whistle. Wrong. At least
There are better ways he could have blown the whistle. Wrong. At least